Learn Blogs
Latest Articles
template
category
category
learn

Data Quality & Data Quality Management (DQM)
In the data age, you must ensure your data is quality data. Learn what that means, and how to achieve it with data quality management.

Security Compliance Auditor Role: Skills and Responsibilities
Learn who security compliance auditors are and how they can make non-compliant systems compliant.
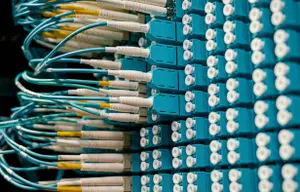
Access Points: A Complete Introduction
All those wireless devices we rely on daily connect thanks to access points, instead of cables and wires. Learn more here.

Fundamentals of Metadata Management
Metadata management includes a set of processes, policies, and technologies that govern how metadata is managed within an organization.

The System Architect Role: Skills, Responsibilities & Salaries
A system architect is a professional who designs and oversees the structure of complex systems. Learn how you can become one.

Log Files: Definition & Introduction
Discover the importance of log files in development and production environments, their types and formats, best practices, and tools for log file analysis.

What Is ISO 42001 for AI?
ISO 42001 is a standard for establishing, implementing, maintaining, and continually improving your Artificial Intelligence Management System (AIMS).

Log Analysis: A Complete Introduction
Learn what log analysis is, explore key techniques and tools, and discover practical tips to effectively analyze system log files.

What Is IoT Security? A Complete Overview
IoT security is a threat protection mechanism and cybersecurity strategy that defends IoT devices against vulnerabilities.