Splunk Named a Leader in the 2022 IDC MarketScape for SIEM
Security Olivia HendersonSplunk has been named a Leader in the IDC MarketScape: Worldwide SIEM 2022 Vendor Assessment (doc #US49029922, November 2022).
We believe this recognition is a testament to our commitment to delivering a best-in-class, data-centric security analytics solution that helps our customers accelerate threat detection and investigations, and achieve cybersecurity resilience.

(IDC MarketScape vendor analysis model is designed to provide an overview of the competitive fitness of ICT suppliers in a given market. The research methodology utilizes a rigorous scoring methodology based on both qualitative and quantitative criteria that results in a single graphical illustration of each vendor’s position within a given market. The Capabilities score measures vendor product, go-to-market and business execution in the short-term. The Strategy score measures alignment of vendor strategies with customer requirements in a 3-5-year timeframe. Vendor market share is represented by the size of the icons.)
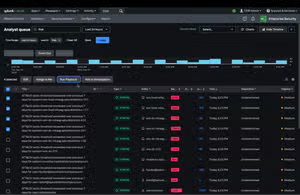
In order to address the myriad of pain points the SOC faces, Splunk Enterprise Security is habitually delivering new features and capabilities to strengthen cybersecurity. Some recent innovations include:
- Risk-based alerting enhancements to transform large volumes of noisy alerts into fewer high-fidelity incidents, prioritized by risk attribution.
- Integration with Splunk Intelligence Management (formerly TruSTAR) to help analysts quickly understand threat context, prioritize triage and accelerate investigations.
- Threat research and detections developed by the Splunk Threat Research Team to help the SOC stay one step ahead of emerging threats.
- Federated Search across distributed environments, on-premises or in the cloud, bringing valuable distributed data to security use cases or performing threat hunting on remote data sets at scale using data models and stats.
- Data Manager for Splunk Cloud lets you onboard data from multiple services and accounts quickly. Ingest and normalize data from AWS, Azure, and soon Google Cloud Platform easily and utilize multi-cloud security monitoring dashboards that build on this data.
- Dashboard Studio helps the creation of dashboards without needing to write code or XML with sample dashboards available from the example hub.
- Creation of the Open Cybersecurity Framework, which helps define a common schema for data flowing in from security tools.
The IDC MarketScape report recognized specific strengths for Splunk, including:
- Splunk has a large number of connections with third-party security tools in enterprise security. Overall, there are over 1,400 data source integrations and 2,700+ applications available on Splunkbase.
- The broad data platform Splunk offers provides many entry points into an organization. More than 90 of the Fortune 100 companies use Splunk in some way. Once Splunk gains a foothold in one area, Splunk use cases expand, possibly at first augmenting another SIEM before the security team moves to use Splunk as its only SIEM.
- Splunk works across multiple clouds as well as in hybrid environments.
- Security professionals are familiar with Splunk, its Search Processing Language (SPL), and/or have Splunk certifications. The Splunk community is a large and engaged one.
To our customers and partners, thank you again for making this recognition possible. Download your complimentary excerpt copy of the 2022 IDC MarketScape for SIEM today to learn more about Splunk Enterprise Security, visit our website or take a tour.
Related Articles

What’s Cyber Security Week like for Splunk? it-sa gold!
Hunting for Malicious PowerShell using Script Block Logging