UEBA Superpowers: Simplify Incident Investigations to Increase SOC Efficiency
Security Fernando JorgeIn an era marked by an increasing volume and sophistication of cyber threats, the efficiency of your SOC operations has become more important than ever. SOCs are flooded by a daily barrage of attacks and alerts, with a significant portion being false positives, leading to alert fatigue and the potential for genuine threats to slip through the cracks. Security teams are so overwhelmed by the sheer volume of attacks that they have reached, if not exceeded, their capacity to effectively and rapidly investigate all of them, every day. As a result, analysts are simply ignoring 41% of those daily alerts. This results in a slow mean time to detect (MTTD) and dwell times of about 2.24 months.
Furthermore, the sophistication of advanced insider threats demands a large volume of time-consuming, human fueled detective work in order to detect, investigate, and respond to these threats. If performed manually, that work is simply not achievable or scalable unless the SOC employs an army of security analysts and data scientists.

Transforming SOC Efficiency
According to the Splunk Security Predictions 2024 report, 86% of CISOs believe AI — a key component of Splunk User Behavior Analytics (UBA) — will alleviate skills gaps and talent shortages, addressing one of the most pressing challenges in cybersecurity today. Here's how Splunk UBA addresses the core aspects of SOC efficiency enhancement.
Automating Threat Detection and Prioritization
- Machine Learning and Anomaly Detection Models: Splunk UBA leverages over 250 machine learning algorithms and anomaly detection rules to sift through vast amounts of data. These models recognize patterns of behavior that deviate from established norms, significantly reducing the manual effort required in the initial stages of threat detection.
- Behavioral Analytics: By analyzing the behavior of users, devices, and applications, Splunk UBA can detect subtle signs of insider threats or compromised accounts that traditional security tools might miss. This approach allows for the detection of sophisticated threats that do not match known signatures or patterns.
- Prioritization of Threats: Through its advanced analytics, Splunk UBA assigns a risk score to detected anomalies, helping SOC teams prioritize their response efforts based on each threat's severity and potential impact. This ensures that the most critical threats are addressed first, optimizing the use of limited SOC resources.
Enhancing Investigative Capabilities
- Detailed Attack Chain Insights: Splunk UBA provides SOC teams with comprehensive insights into the attack chain, offering detailed context around each detected threat. This includes information on how the threat entered the system, what it has affected, and potential next steps for the attacker. In fact, in Splunk UBA’s “Kill Chain” menu, analysts can see when anomalies were seen in the environment, and how they map to each stage of the kill chain. Analysts can see anomalies occurring during the intrusion, lateral movement and expansion, and exfiltration. This gives analysts a more holistic view, thereby streamlining the investigation and response process.
- Integration with Splunk Enterprise and Splunk Enterprise Security (ES): Splunk UBA enhances existing security infrastructure by seamlessly integrating with Splunk Enterprise Security (ES). It enriches security data with behavioral insights, making it easier for SOC teams to correlate alerts and automate aspects of the investigation and response process. Also, by combining Splunk User Behavior Analytics’ multi-entity, behavior-based anomaly and threat information with Splunk Enterprise Security’s correlation rules and searches, security teams can establish a potent and wide-reaching defense against the most sophisticated threats. Splunk User Behavior Analytics automatically pushes threat information into Splunk Enterprise Security to create a centralized incident view and an end-to-end investigative workflow.
Achieving SOC Efficiency Gains
- Reduction in False Positives: By intelligently analyzing behavior to identify genuine threats, Splunk UBA significantly reduces the number of false positive alerts that SOC teams must investigate. This allows analysts to concentrate on actual threats, improving response times and overall SOC productivity.
- Streamlined Incident Investigations: Splunk UBA's analysis and prioritization capabilities simplify the incident investigation process. SOC teams can quickly understand a threat's nature, potential impact, and the necessary steps for mitigation, reducing the overall time and effort required for incident resolution.
In conclusion, Splunk UBA empowers SOCs to navigate the evolving threat landscape more effectively, transforming the approach to cybersecurity from reactive to proactive. By automating the detection and prioritization of threats, enhancing investigative capabilities, and streamlining SOC operations, Splunk UBA enables organizations to safeguard their digital assets more efficiently and effectively.
To learn more about Splunk UBA and how it can strengthen security for your organization, visit the Splunk UBA website, take a tour of the product, explore our Essential Guide to UEBA, or connect with a Splunk security consultant. Read the other blogs in this series to learn more about how Splunk UBA’s detection capabilities and visibility features can help your organization defend against the latest stealthy threats.
Related Articles
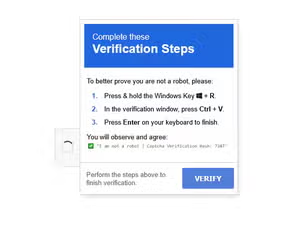
Beyond The Click: Unveiling Fake CAPTCHA Campaigns

Threat Update: Cyclops Blink
